A post appeared on the Pikabu portal about a possible security issue in the Max messenger. The user claims that photos he sent in private messages through the web version became publicly accessible.
According to the author, if an attacker knows the exact web address of an image, they can view it without authorization: there is no need to be the recipient of the file within the system. The user claims that this works similarly to ordinary image-sharing websites, only with a longer link.
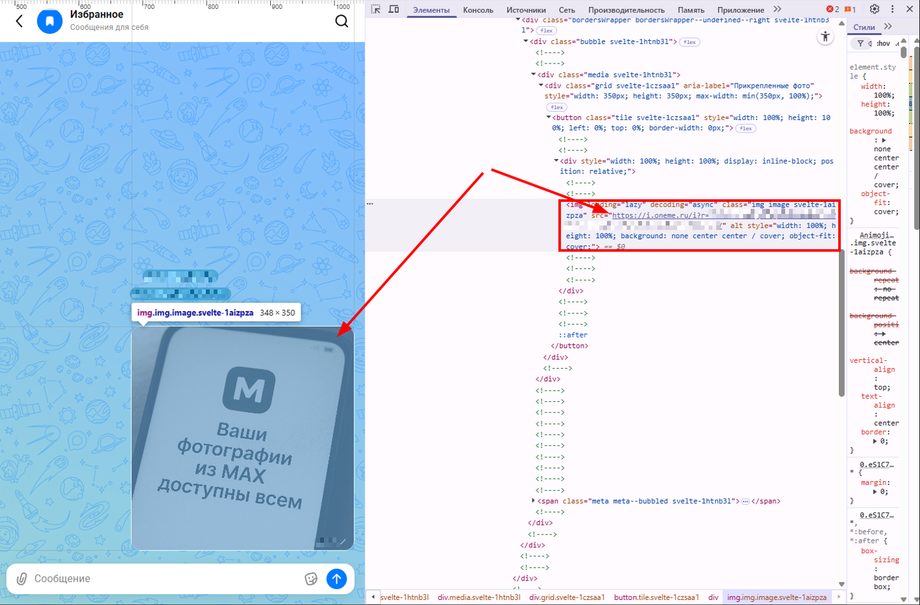
The author also suggests that automated data collection systems, including foreign ones, could theoretically gain access to random user images by brute-forcing a key consisting of several dozen characters.
And the cherry on top: even if you delete the image from the chat, it still remains accessible via the link without authorization, for at least a week for sure; I did not check any longer. I appeal to the developers — fix this misunderstanding!
Earlier, Max repeatedly denied rumors about vulnerabilities in the messenger. The day before, the company commented on information that had appeared in the media claiming that the messenger allegedly tracks VPN users and communicates with WhatsApp and Telegram servers. Max stated that such requests do not exist, and that IP addresses are used only for the proper operation of calls. As for requests to Google and Apple servers, they are needed solely to verify the delivery of push notifications and do not affect personal data, the developers emphasized.
Read more materials on the topic:
- Max conquers the world: the messenger is now available in 40 countries
- The absence of a building chat in Max will be punishable by a fine
- Stores will be required to accept Max ID for data verification starting in autumn 2026