
Suspicious activity is detected by analyzing the device's power consumption

Suspicious activity is detected by analyzing the device's power consumption

These messages contain a link to a file in .vcf format

An elderly woman fell victim to telephone scammers who introduced themselves as employees of government agencies

Fraudsters are masquerading as support for the state messenger

Kaspersky NGFW 1.0 Combines Software and Hardware

Scammers offer to return money for paying taxes and demand codes from SMS

Fraudsters demand to update data by phone

Instead of selling stolen data, hackers now seek to disrupt the operation of organizations
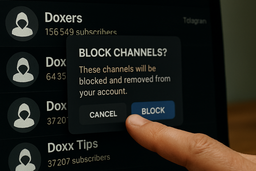
The purge followed numerous user complaints
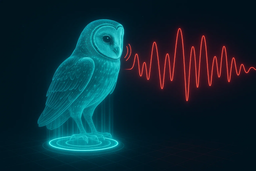
The development is designed to expose fake audio recordings

The scheme consists of two stages using fake calls and fake codes

The list will include taxis, delivery services, marketplaces, and other mass-use services

The investigation received information about the fraudsters from the accused himself

State Duma deputies came up with such a proposal

St. Petersburg court has already blocked two resources mimicking the morgues of the Northern capital